Modern cryptography stands at a pivotal moment. For decades, the security of digital systems has relied on a carefully balanced partnership between symmetric encryption (such as Advanced Encryption Standard) and asymmetric encryption (including RSA and Elliptic Curve Cryptography). While symmetric algorithms provide high-speed data encryption, asymmetric techniques enable secure key exchange and authentication. Together, they form the backbone of protocols like TLS that secure the modern internet.
However, this balance is now under threat. Advances in quantum computing particularly algorithms like Shor’s Algorithm, pose an existential risk to widely used public-key systems. Shor’s Algorithm can efficiently factor large integers and compute discrete logarithms, rendering RSA and ECC fundamentally insecure in a sufficiently powerful quantum environment. This has accelerated a global shift toward post-quantum cryptography (PQC), where new asymmetric algorithms are designed to resist quantum attacks.
In contrast, symmetric cryptography remains comparatively resilient. Quantum algorithms such as Grover’s Algorithm can weaken symmetric encryption, but only quadratically. In practice, this means that doubling key sizes, such as moving from AES-128 to AES-256 can effectively mitigate quantum threats. As a result, symmetric encryption is expected to remain a foundational component of secure systems well into the post-quantum era.
The future, therefore, is not a replacement of cryptographic paradigms but a convergence. Emerging architectures are increasingly adopting hybrid encryption models, combining classical symmetric algorithms with both traditional and post-quantum asymmetric techniques. For example, next-generation systems may use lattice-based key encapsulation mechanisms (such as Kyber) to establish secure keys, while continuing to rely on AES for high-performance data encryption. This hybrid approach ensures backward compatibility while enabling forward security against quantum adversaries.
Equally important is the concept of cryptographic agility the ability of systems to dynamically transition between algorithms as threats evolve. In a world where today’s secure standard may become tomorrow’s vulnerability, static cryptographic designs are no longer sufficient. Cloud platforms, large-scale infrastructure, and distributed systems must be architected with modular cryptographic layers that can adapt without requiring complete system overhauls.
For infrastructure architects and security engineers, this transition introduces both challenges and opportunities. Migrating to hybrid and post-quantum systems involves rethinking key management, protocol design, and performance trade-offs at scale. Yet it also provides a pathway to build resilient, future-proof systems capable of withstanding not only classical adversaries but also the emerging quantum threat landscape.
Ultimately, the evolution of cryptography is not about abandoning the past, but about intelligently extending it. Symmetric encryption will continue to provide speed and efficiency, asymmetric cryptography will evolve to resist quantum attacks, and hybrid models will bridge the two. The organizations that embrace this transition early designing for agility, scalability, and quantum resilience will define the next generation of secure digital infrastructure.
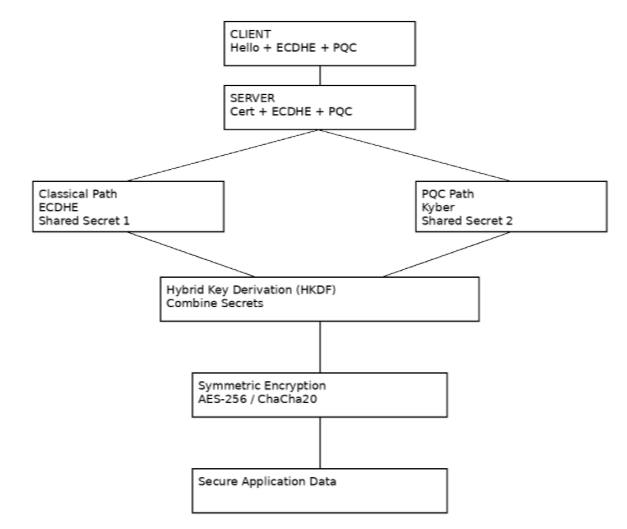
Hybrid TLS + PQC Architecture
┌──────────────────────────────┐
│ CLIENT │
└─────────────┬────────────────┘
│
│ 1. Client Hello
│ - Cipher Suites
│ - ECDHE Key Share
│ - PQC (Kyber) Key Share
▼
┌──────────────────────────────┐
│ SERVER │
└─────────────┬────────────────┘
│
│ 2. Server Hello
│ - Certificate (Public Key)
│ - ECDHE Response
│ - PQC (Kyber) Response
▼
┌────────────────────────────────────────────────────┐
│ DUAL KEY EXCHANGE LAYER │
│ │
│ Classical Path Post-Quantum Path │
│ (ECDHE) (Kyber) │
│ │ │ │
│ ▼ ▼ │
│ Shared Secret 1 Shared Secret 2 │
│ │
└───────────────┬────────────────────────────────────┘
│
▼
┌────────────────────────────────────────────────────┐
│ HYBRID KEY DERIVATION FUNCTION (HKDF) │
│ │
│ Combines: Classical + PQC Secrets │
│ → Produces Unified Session Key │
└───────────────┬────────────────────────────────────┘
│
▼
┌────────────────────────────────────────────────────┐
│ SYMMETRIC ENCRYPTION LAYER │
│ │
│ AES-256 / ChaCha20 │
│ (Bulk Data Encryption) │
└───────────────┬────────────────────────────────────┘
│
▼
┌────────────────────────────────────────────────────┐
│ SECURE APPLICATION DATA FLOW │
│ │
│ Encrypted HTTP / API / Cloud Traffic │
└────────────────────────────────────────────────────┘